What is OS command injection, and how to prevent it?

By A Mystery Man Writer
In this section, we explain what OS command injection is, and describe how vulnerabilities can be detected and exploited. We also show you some useful
EXPLOITING OS COMMAND INJECTION VULNERABILITIES, by Hashar Mujahid
What is SQL Injection and How to Prevent It? - PCI DSS GUIDE
A Pentester's Guide to Command Injection
Web Application Injection Cheat sheet - Abricto Security
Blind OS Command Injection via Activation Request!!, by theUnixe

Back to Basics: OS Command Injection

Mandar Parab on LinkedIn: Successfully completed the Ethical Hacking training from Internshala…

What is OS Command Injection, and How to Prevent It #oscommandinjection #os #operatingsystem

API HACKING” PART-11, OWASP TOP 10, Command Injection Vulnerability, by Madhumathi chamarthi

Mandar Parab on LinkedIn: Task_3
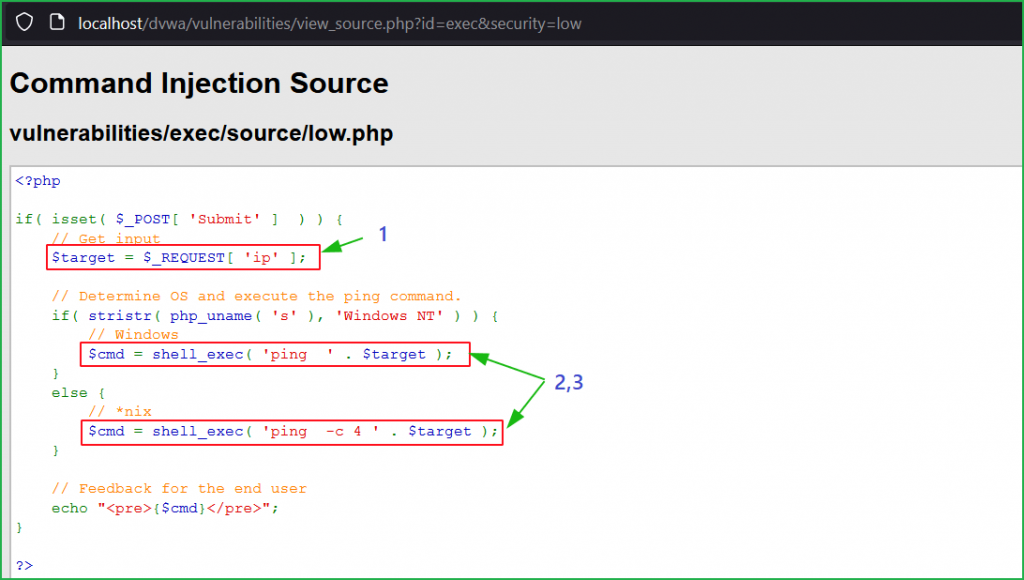
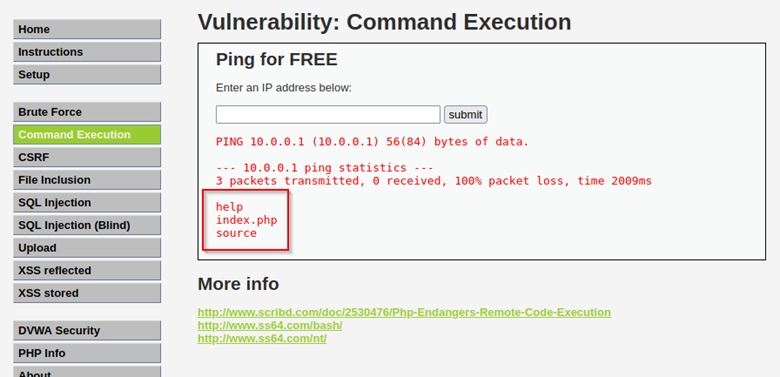
DVWA Command Injection

Risk Management Assessment and Control - Risk Management Assessment and Control Managing Risk - Studocu
Os Command İnjection Açığı Nedir ?

Behind the Scenes of OS Command Injection Attacks, by Venkata Sai Manikanta Manugula
Black Hunter (f0rever_hunter@) / X
:format(webp)/https://static-my.zacdn.com/p/cos-3637-4404692-4.jpg)

/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2021/s/7/hZElXLQcAcfPBDUfJCbQ/2015-05-27-app-012.jpg)